|
A cluttered digital space can lead to stress, decreased productivity, and even make you more susceptible to cyber threats. So, let’s dive into the comprehensive guide to mastering your digital wellbeing this spring with our ultimate cyber spring-cleaning series. | ↑ |
|
Our Threat Labs recently exposed a highly sophisticated malware operation known as “GuptiMiner”, which targets corporate networks specifically. Our team of experts got into research mode right away! | ↑ |
|
The air is electric, the skies are clear, and the lineups are out – festival season is upon us! From the euphoric beats under starlit skies to the communal spirit of like-minded souls, festivals offer a world apart, a temporary escape into a realm of music, art, and shared experiences. | ↑ |
|
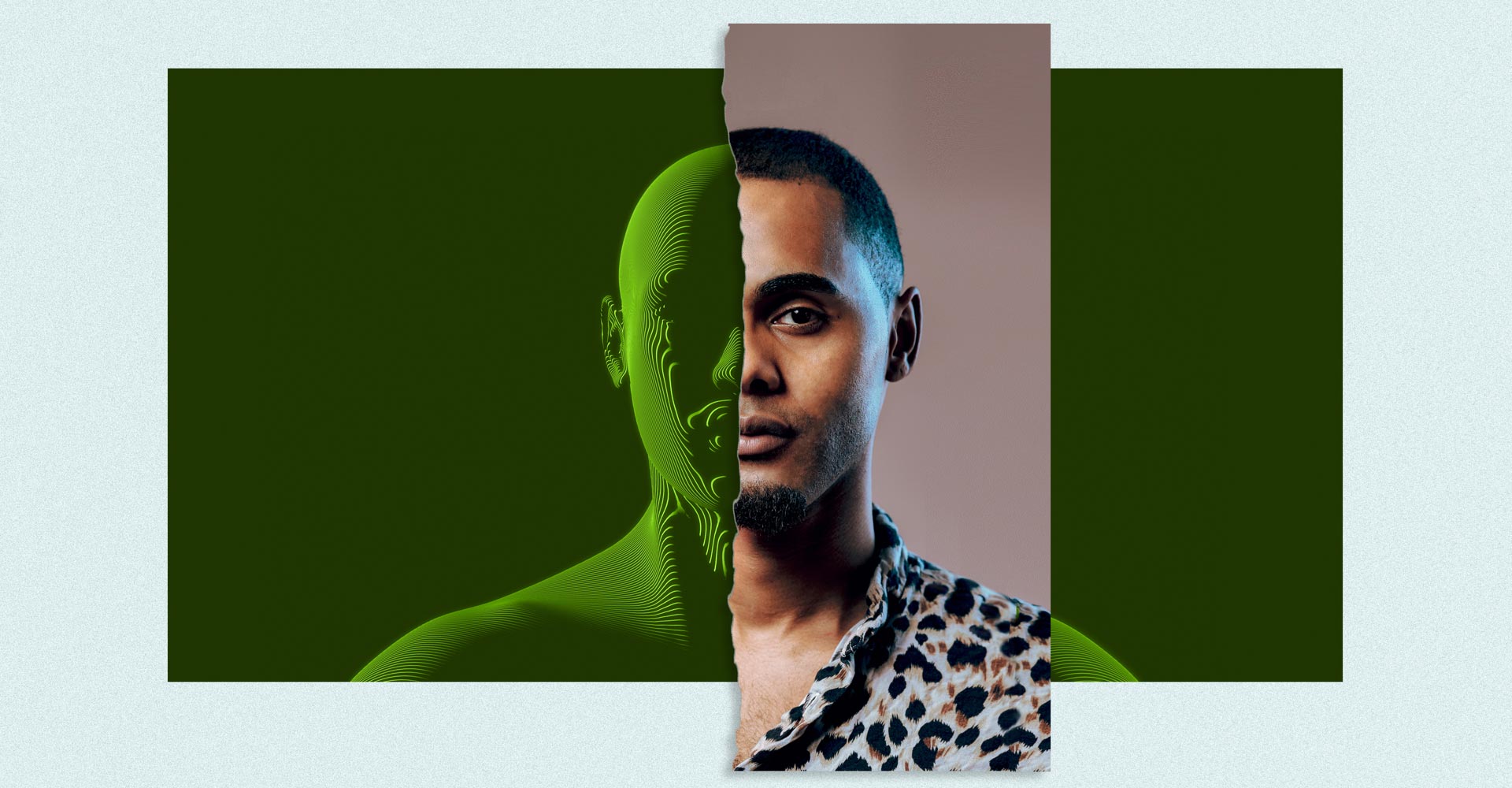
In the ever-evolving landscape of the digital world, safeguarding your online presence has become more a necessity than a choice. However, when it comes to online safety, performance, and privacy, one size does not fit all. This is where Avast One Silver shines, offering you "All-in-one; the way you want it." It's about having the power to tailor your digital protection to match your lifestyle, without the clutter of unwanted features??. | ↑ |
|
Today’s most common crime is not burglary, car theft or even shoplifting - it’s online fraud. And this includes pitfalls such as emotional scamming. Not to mention, anyone with an internet connection (in other words, all your customers) is a potential victim. So what do you need to know, and how can you advise your customers, to help keep them safe online from this particular kind of scam? | ↑ |
|
Tax season is upon us, and you know what that means: It’s time for IRS scams to start showing up. These scams take the form of anything from phishing emails to fake phone calls — and they can be difficult to spot. | ↑ |
|
Financial scams are like that one guest at the party who just won't leave, constantly evolving and finding new ways to crash our digital lives. Lately, they've taken a turn for the futuristic with AI-generated videos popping up in investment scams. | ↑ |
|
We are excited to announce our new flexible billing option for our Managed Service Providers (MSPs) using the Multi-company partner version of our cloud management platform, the Avast Business Hub. This pay-as-you-go feature helps MSPs consume Avast Business solutions in the way that best aligns with how they transact with their end customers. | ↑ |
|
Have you ever gotten a call from the IRS? If you have, then you might be one of the thousands of people losing millions of dollars every year to IRS scam calls. These fraudulent calls, which claim to be from the Internal Revenue Service (IRS), are typically made by scammers who are trying to steal money or personal information from taxpayers. | ↑ |
|
PDFs have become synonymous with convenience and reliability, serving as the backbone for our document-sharing needs. Whether for work, school, or personal use, their ability to maintain formatting across various platforms has made them indispensable. | ↑ |